11 Best Practices for Writing Secure Java Code
Nowadays, security is an important aspect that businesses should never overlook. The rise in cyber-attacks and data breaches has made security even more crucial. Therefore, it is important to understand java code practices that help businesses in maintaining their security. However, when you hire a Java developer with great java expertise, it can also be helpful for the businesses to secure their applications.
In this article, we will discuss the top 11 Java security best practices used by Java developers.
Why is Java a secure code?
Java security is a collection of APIs, tools, and implementations of commonly used security algorithms, mechanisms, and protocols. Java security APIs cover a wide range of areas, including cryptography, public key infrastructure, secure communication, authentication, and access control.

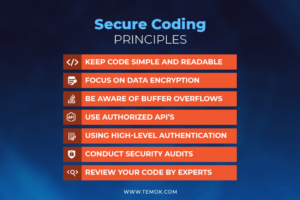
List Of The Best Practices to Secure Java Code
Here is the list of the best practices to secure java code-
Use Strong Authentication Mechanisms
The first step in securing your application is to use strong authentication mechanisms. Passwords are no longer secure enough; you should use multi-factor authentication or biometric authentication to enhance the security of your application. When users log in, they should be required to provide more than one form of authentication, such as a password and a fingerprint.
Validate Input
The second best practice is to validate input. Input validation is the process of checking data that is being entered into the system to ensure that it is valid and not malicious. This helps to prevent attacks such as SQL injection and cross-site scripting. Developers ensure that they validate input in your application.
Use Secure Communication Protocols
Another important best practice is to use secure communication protocols. The use of SSL or TLS is essential in securing communication between the client and server. This helps to prevent man-in-the-middle attacks and data interception. Java developers ensure that they use secure communication protocols in your application.
Implement Authorization and Access Control
Authorization and access control are critical to securing your application. Access control determines who can access the application and what they can do. Authorization determines the actions that the user can take based on their level of access. This helps to prevent unauthorized access and data breaches.
Encrypt Data
Data encryption is essential in securing sensitive data. Encryption involves converting plain text into ciphertext using an algorithm. This ensures that even if the data is intercepted, it cannot be read without the encryption key. When you hire a Java developer, ensure that they encrypt sensitive data in your application.
Use a Firewall
A firewall is a network security system that monitors and controls incoming and outgoing network traffic. It acts as a barrier between the network and the internet.
Implement Proper Error Handling
Proper error handling is critical in securing your application. Error messages should not reveal sensitive information and should provide enough information to help users troubleshoot.
Patch and Update Regularly
Patching and updating are critical in securing your application. Software vulnerabilities are constantly being discovered, and patching and updating ensure that your application is protected from these vulnerabilities.
Use Secure Password Storage
Password storage is a crucial aspect of security. Passwords should not be stored in plain text, and they should be encrypted. Hashing is a popular technique used to store passwords. Developers ensure that they use secure password storage in your application.
Test and Verify Security
Testing and verification are crucial in ensuring that your application is secure. You should regularly test and verify the security of your application to identify vulnerabilities and address them..
Use Security Libraries
There are many security libraries available for Java developers. These libraries provide pre-built security features that can be easily integrated into your application.
These practices are a must to protect your Java code. So, if you hire web developers to do the job, ensure that they have the right skills and knowledge to implement these.
Why Java Code Security Matters?
Creating secure and reliable code is crucial for each developer and business as Java-based attacks increase in frequency.
- Reducing the risk of assaults is made possible by securing your Java code. The chance of a data breach will be lower the more secure your code is.
- Safeguard your data. By providing your sensitive data with an additional layer of security, encryption can assist you in minimizing the harm caused by an effective attack.
- Get rid of typical weaknesses quickly. It will be much simpler for you and your organization to remain on top of vulnerabilities if you adhere to Java secure coding best practices and standards.
- Spend less. Prevention is always better than therapy. Yet again, resolving vulnerabilities before the worst occurs will lower all potential costs associated with a leak of sensitive user and/or customer data.
5 Java Security Tools and Commands
Java security tools and commands have become increasingly important in order to ensure that Java applications are protected against malicious attacks.
In this section, we will discuss some of the most popular Java security tools and commands that can be used to enhance the security of Java applications.
Keytool
Keytool is a command-line tool that is used to manage public and private key pairs, digital certificates, and keystores. It is an essential tool for securing Java applications as it helps to create, manage, and store the cryptographic keys that are used to secure data and communication between different systems.
Jarsigner
Jarsigner is another command-line tool that is used to digitally sign Java archives (JAR files). Digital signatures are used to verify the authenticity and integrity of the JAR files, and they can be used to ensure that the JAR files have not been tampered with.
JConsole
JConsole is a graphical tool that is used to monitor and manage Java Virtual Machines (JVMs). It can be used to monitor the performance of the JVM, identify memory leaks, and optimize the performance of the application.
Java Security Manager
Java Security Manager is a security tool that provides a sandbox environment for Java applications. It can be used to restrict the permissions of Java applications and prevent them from accessing sensitive resources on the system.
Java Cryptography Extension (JCE)
Java Cryptography Extension is a security tool that provides support for advanced cryptographic algorithms, such as AES, DES, and RSA. It can be used to encrypt and decrypt data, as well as to secure communication between different systems.
Summing Up
In a nutshell, security is an essential aspect for businesses and Java application development. If you are looking to hire a Java developer, you should ensure that they have knowledge of and adhere to above-mentioned best practices. By implementing the above practices, businesses can build secure and reliable applications.



